News & Events
Exploring Blockchain Security: Varieties and Characteristics
- 19/06/2024
- Posted by: Upender Yadav
- Category: Uncategorized
No technology can claim to be completely foolproof, and blockchain technology is no exception. It’s important to recognize the potential security challenges associated with blockchain to build trust and encourage its wider use. Just like any other technology, blockchain is susceptible to security threats. To safeguard it from attackers, various security measures are available, and each of them plays a crucial role in ensuring the technology’s safety within organizations.
Blockchain Security
Blockchain security deals with the steps taken to guard against hacking, breaches, and unauthorized entries into blockchain systems. Think of a blockchain as a decentralized digital record that protects data by making sure it can’t be altered or tampered with. But even though it has its own security features, blockchain isn’t completely safe from potential risks.
There are common vulnerabilities in blockchains, like DDoS attacks, flaws in smart contracts, harmful nodes, challenges in keeping private keys safe, and the risk of 51% attacks. To counter these threats, blockchains use various security strategies. This includes protocols to reach agreement, encryption methods, and multiple authentication steps to lessen these risks.
Why Blockchain Security Matters
Many businesses are drawn to blockchain technology because it offers decentralization, transparency, and the assurance that once data is added, it can’t be changed. But to make sure these systems stay trustworthy and reliable, strong security is vital.
Blockchain networks, by using a mix of security measures like agreement protocols, encryption, and multi-step authentication, are able to address these security challenges. They can provide a high degree of protection, effectively shielding against potential security threats.
Simply put, for blockchain technology to thrive and be sustainable in the long run, robust security measures are crucial.
Understanding the Different Types of Blockchains
- Private Blockchain Networks: These are exclusive blockchain networks where joining requires an invitation from a central figure or by adhering to specific criteria. They are often chosen by businesses that require more controlled environments. Members must get permission to participate. In these networks, consensus is typically reached using a “Proof-of-Authority” (PoA) mechanism. Their primary use is for tasks like access control, authentication, and maintaining confidential records.
- Public Blockchains: These are open networks emphasizing inclusivity and transparency. Anyone can participate in transaction validation on public blockchains. Familiar examples include Bitcoin and Ethereum, whose codes are open-source and available for everyone to see. A unique feature of public blockchains is their decentralized nature, safeguarded by cryptographic techniques. Decentralization means there’s no single point of control or failure. Consensus mechanisms in public blockchains generally fall into “Proof-of-Work” (PoW) or “Proof-of-Stake” (PoS). What drives people to contribute is often the potential to earn cryptocurrency, like through mining. Anyone can join and participate, which sets them apart from private networks.
- Consortium Blockchains: These are a middle ground between public and private blockchains. In consortium blockchains, a group of pre-approved entities come together to share a network. They allow for a level of decentralization while retaining some control. The data within might be kept private. Consortium blockchains can use various consensus mechanisms, including PoW, PoA, PoS, and even delegated proof-of-stake. These are ideal for scenarios where participants are known, like in banking transactions, supply chain processes, or IoT applications.
In essence, while public and private blockchains often grab the limelight, consortium blockchains represent a balanced approach, merging both worlds’ benefits.”
Understanding Blockchain Security
Blockchain security is a cornerstone feature that underpins its utility for digital currencies and various other applications requiring trustworthy and transparent data interactions. Let’s delve into how blockchain achieves this secure environment:
- Cryptographic Techniques: One of the primary tools in the blockchain security toolbox is cryptography. Tools like hash functions and digital signatures play a central role. Hash algorithms generate a unique digital ‘fingerprint’ for each transaction, which is then recorded on the blockchain. This ensures that data is genuine and hasn’t been tampered with. Digital signatures confirm the authenticity of a transaction by validating that it came from a particular user.
- Consensus Protocols: Blockchains don’t just rely on cryptographic measures alone. They also utilize consensus protocols, which are rules and methods the network uses to agree on the contents of the blockchain. This ensures that all participants have a consistent version of the blockchain, further securing the data against tampering.
- Smart Contracts: These are self-executing contracts where the terms of the agreement are written directly into lines of code. They automate and ensure that parties stick to the stipulated terms, minimizing the risk of fraud.
In essence, blockchain security harnesses a combination of cryptographic techniques, consensus protocols, and smart contracts to ensure data remains untainted and free from unauthorized alterations.
Key Elements of Blockchain Security
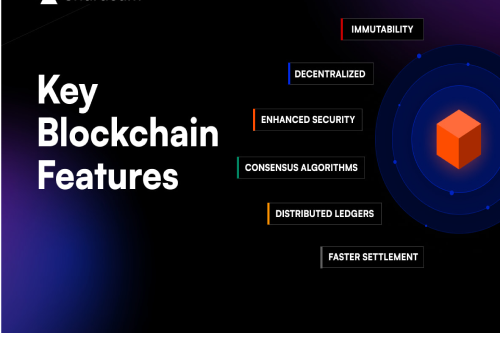
Blockchain technology offers unparalleled security features, becoming an invaluable asset for numerous organizations. Let’s dive into the core characteristics that enhance the safety and effectiveness of blockchains:
- Distributed Network: One of the hallmarks of blockchain is its distributed nature. By operating on a network of dispersed nodes, it eliminates any single point of vulnerability. This design provides resilience against targeted attacks, ensuring the network remains intact even if a few nodes are compromised.
- Transparency in Transactions: Every transaction on a blockchain is visible to all network participants. This transparent design allows every node to track and verify each transaction. Such visibility acts as a deterrent to malicious activities, guaranteeing that all users have access to uniform, reliable information.
- Consensus Mechanism: Transactions on a blockchain aren’t recorded instantly. They first undergo a validation process where multiple nodes verify their authenticity. Once consensus is achieved, the transaction is added to the blockchain. This collective validation ensures the accuracy and trustworthiness of each transaction.
- Cryptography: At the heart of blockchain security is cryptography. Using advanced mathematical algorithms, each transaction is encrypted, ensuring its confidentiality and integrity. Given that every transaction is linked to its preceding one, altering any transaction data becomes a herculean task, offering robust protection against tampering.
In a nutshell, these core features make blockchain an epitome of security in the digital realm, providing confidence to organizations and users alike.
Applications of Blockchain Security
Blockchain’s secure nature lends itself to a variety of applications. Here are some prominent use cases where blockchain security plays a pivotal role:
- Cryptocurrency Transactions: Most people’s introduction to blockchain is through cryptocurrencies like Bitcoin and Ethereum. By using a decentralized blockchain system, these digital currencies provide secure and transparent transactions without the need for intermediaries like banks.
- Supply Chain Management: In supply chains, tracking the origin and movement of goods can be complex. Blockchain introduces transparency and security to this process. Each step, from production to delivery, is recorded, ensuring that goods’ origins and routes can be verified with confidence.
- Identity Verification: Verifying the identity of individuals and entities is vital in many sectors. Blockchain can securely store identification data, ensuring that only authorized personnel have access. This has potential applications in areas like voting, banking, and healthcare, providing a tamper-proof method of identification.
- Smart Contracts: Think of smart contracts as automated agreements that self-execute when certain conditions are met. Because they’re built on blockchain, they’re transparent and secure. This makes them ideal for sectors like real estate, where contracts are essential but often bogged down by administrative delays. In the financial world, insurance claims can be processed via smart contracts, ensuring quick and transparent claim settlements.
In essence, these use cases highlight how blockchain security is revolutionizing traditional systems, making processes more secure, transparent, and efficient.
Challenges in Blockchain Security
While blockchain has many inherent security features, it also faces specific challenges that need to be addressed:
- Regulatory Absence: Blockchain technology is still evolving, and legislative bodies are racing to catch up. Without well-defined regulations in place, malicious actors can exploit vulnerabilities with less fear of legal consequences.
- Interoperability Issues: Different blockchain systems follow different standards and protocols. This diversity, especially at this early stage of blockchain evolution, means there can be security lapses when data is transferred across differing blockchains.
- 51% Attacks: One of blockchain’s foundational principles is that no single entity should have dominant control. However, if a malicious actor gains more than 51% of a network’s computing power, they can potentially rewrite the blockchain’s history and double-spend coins, undermining the system’s integrity.
- Mismanagement of Private Keys: Private keys are like the passwords to a user’s digital assets on the blockchain. It’s crucial to protect them. However, many users are unfamiliar with secure private key storage practices, leading to potential vulnerabilities. If lost or stolen, assets associated with that key could be irretrievably compromised.
In sum, while blockchain offers a more secure system than traditional databases in many ways, it isn’t foolproof. Recognizing and addressing its vulnerabilities is crucial for its long-term success and adoption.
Conclusion
Blockchain technology stands at the forefront of redefining sectors like finance, supply chain management, healthcare, among others. Its promise of transparent, secure, and streamlined digital transactions paves the way for a future where data interactions are trustworthy and efficient. However, as with all innovations, the journey is a continuous one. Ensuring its security and addressing challenges will be pivotal in harnessing the complete power and potential of blockchain. The road ahead is promising, and with a sustained focus on strengthening its security, the horizon seems bright for blockchain’s transformative impact.
Trending Courses
Popular Courses
Categories
The certification names and logo are the trademarks of their respective owners




